White Papers (IGA, Authentication, SSO, Web SSO, HA)
Evidian
ID Synchronization for a multi-directory identity repository
User information is often stored in many places: Active Directory, HR applications, Oracle and SQL Server, e-mail base, LDAP sources… How can you get a single, reliable identity repository? By reconciling existing sources automatically, directory synchronization can help you maintain a central identity repository for all your users.
Analytics & Intelligence
Evidian Analytics and Intelligence strengthens the Evidian Identity and Access Management Suite (Evidian IGA, Evidian Enterprise SSO, Evidian Authentication Manager and Evidian Web Access Manager). Developed for middle-sized and large organizations, it complements your Evidian solution.
Next generation identity and access management for Industrial Internet of Things and Industry 4.0
English French
This white paper addresses the challenges for Identity and Access Management (IAM) in the context of IT and OT convergence and introduces concepts and architectures for thenext generation of IAM for the Industrial Internet of Things.
IAM at the heart of the zero trust approach
Often, an organization’s first instinct is to implement zero trust at the network level by reinforcing access to company resources, particularly via VPN for remote workers. However, in the event of an intrusion on the company network, access to information depends entirely on user access rights. It is therefore necessary to manage these access rights to ensure minimal user privileges.
Executive view Identity as-a-Service (Orbion)
This report reviews the Evidian Orbion solution, which is recognized as a complete IAM & cloud based (IDaaS) solution.
Overall leader on Identity Governance & Administration
KuppingerCole has positioned Evidian IGA and IDaaS as an overall leader, product leader, innovation leader, market leader among 25 IGA product vendors in its latest Leadership Compass report focused on Identity Governance & Administration.
Best single sign-on solutions
According to KuppingerCole : “Evidian is highly experienced in providing smooth, proven, secure solutions for E-SSO. […] Evidian is among the clear Leaders in the E-SSO market segment and a logical pick for shortlists in that area”
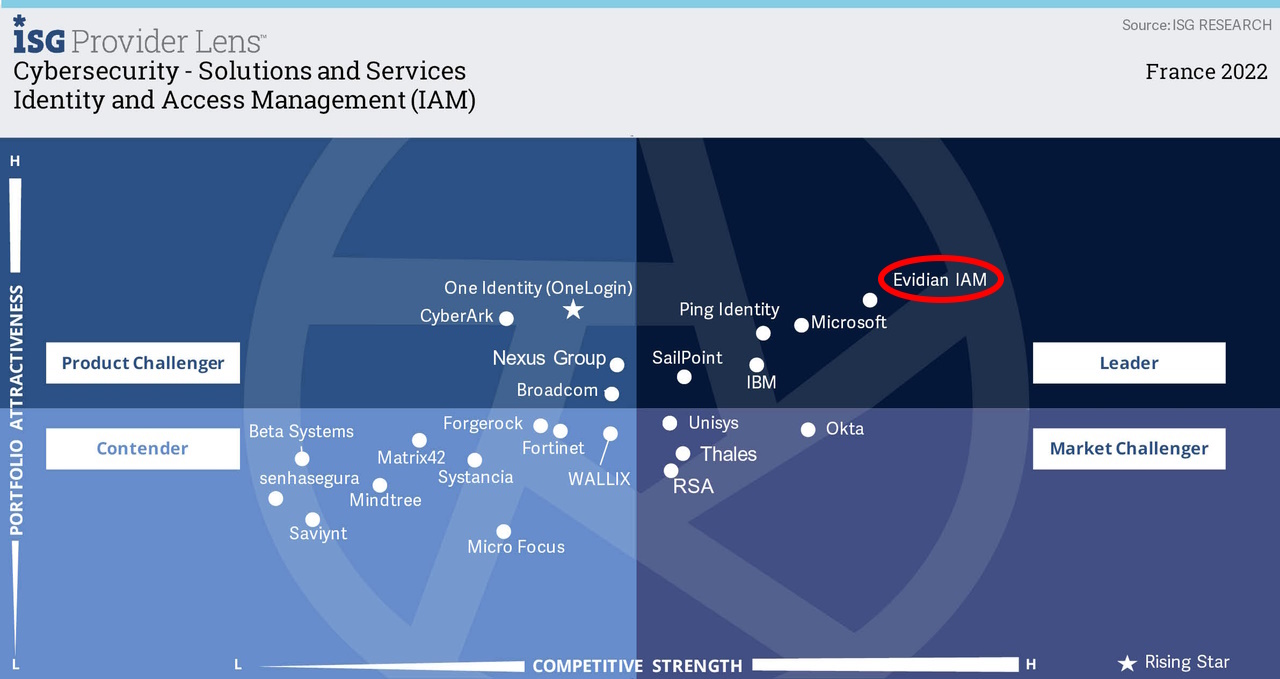
Who are the leaders of IAM cybersecurity solutions?
Evidian IAM is positioned in the cybersecurity quadrant as leader in Identity and Access Management in the U.S. Public Sector, the German market and the French market by ISG, a leading advisory firm.
The Benefits of a One-Stop Shop for a Modern, Unified, and Agile IAM Approach
This report describes how Evidian meets the needs of organizations in the digital age, and how these organizations should gradually modernize the existing IAM legacy.
Executive View - Evidian Identity & Access
This report reviews the Evidian Identity and Access Management solutions.
European Identity & Cloud Award Best Identity and Access Management Project: Nantes University Hospital
In this report, discover why the Nantes university hospital was awarded for its innovative approach in identity and access management (IAM) with Evidian.
Maintaining HIPAA Compliance with Identity and Access Management solutions
This white paper explains how, based on Atos expertise on the HIPAA regulation, identity and access management solutions can help Covered Entities remain compliant and safeguard Protected Health Information (PHI).
Evidian Enterprise Access Management and 21 CFR Part 11
This document explained in a table, how Evidian Enterprise Access Management answer to each requirement of the 21CFR Part 11 paragraph.
Orbion
Evidian takes care of everything related to your Identity and Access Management with Orbion (Identity as a Service)
Learn more >
Identity Governance and Administration
Manage access and authorization of all your users in your company
Learn more >
Web Access Manager
Gateway for web apps with SSO, multi-factor authentication, identity federation
Learn more >
Authentication Manager
Authentication Manager
Enterprise multi-factor & passwordless authentication on Windows PCs
Learn more >
Enterprise Single Sign-On (SSO)
Secure access to legacy and web apps on PCs & mobiles with SSO