-
Analytics
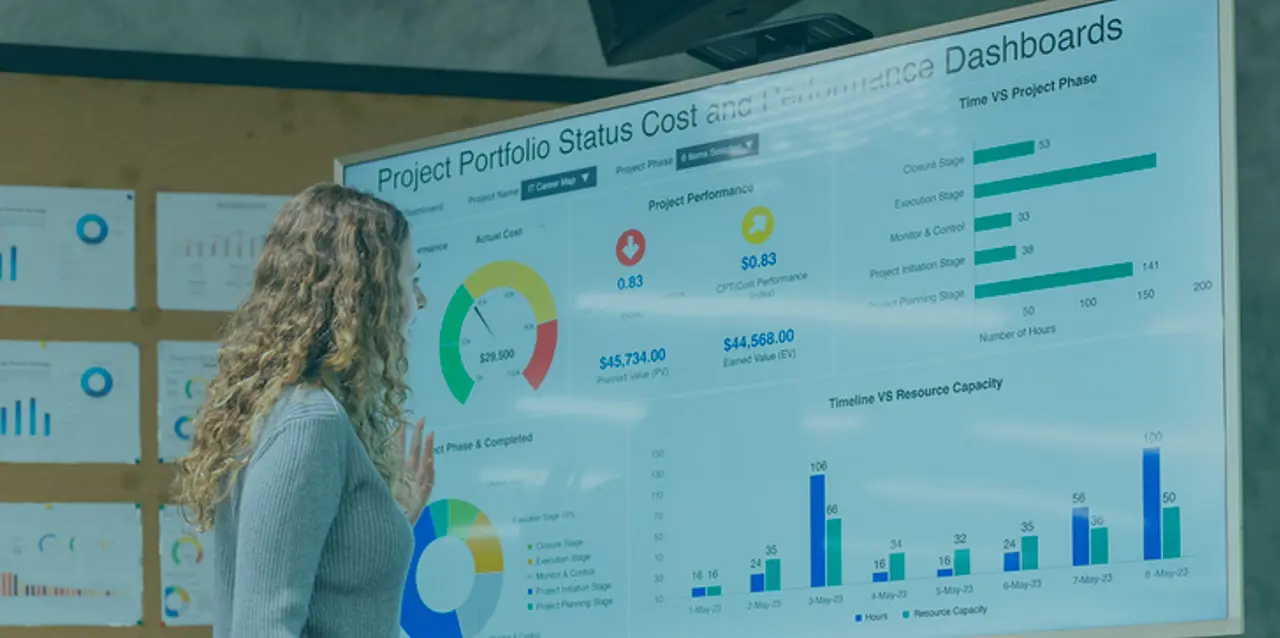
Monitoring and powerful reporting for regulatory compliance
-
Analytics Options
- Data-driven Identity and Access Management
- Working with Evidian's IAM solutions (on-Premises and SaaS)
Effective cybersecurity now demands automation and analytics to work in conjunction for threat identification, mitigation and management. As businesses move to become digital enterprises they must continually scrutinize their operations, security processes and IT environments.
Fixing pain points
Global cybersecurity risks are increasing. According to a 2021 study by SafeGuard Cyber & Pulse : lack of visibility is the biggest challenge for security leaders who aim to maintain security and compliance across all business communications. Another study done by Strata Identity (State of Multi-Cloud Identity Report) in 2023 has found out that over 75% of enterprises do not know where applications are deployed and who has access.
For more informations contact us.
And detecting threats
Security and compliance are daily issue when it comes to Identity and Access Management. In an increasingly risky environment for corporations, CISOs and Administrators need enhanced processing and analysis capabilities to leverage and review data produced by their IAM systems and investigate security events related to users’ lifecycle and entitlements usage..

Identity Analytics
Identity analytics is an option of Identity and Access Management products. The combination of big data and advanced analytics improves identity governance and administration processes through the continuous monitoring of your environment of risk. Using analytics techniques increases the effectiveness of access certification and access rights policy management by highlighting Key Risk Indicators (KRIs) to detect high-risk users, excessive access, dormant or orphaned accounts and abnormal user behaviors.
Customer Benefits
Easily identify risks
The performance indicators provided with the product allow you to monitor activities considered to be at risk, whether done by a user or an administrator, such as Segregation of Duties validations, password changes, direct assignations... Let's see how >>
Track suspicious practices
With the audit analysis functionality, Evidian Analytics places data into your daily operation. Through a business-oriented interface Evidian Analytics allows you to track audit events and find the root cause of practices that you would consider abnormal or outside the normal use of the Identity and Access Management system. Check the features >>
Investigate events and analyze trends
Evidian Analytics allows a fine-grained auditing of your IAM system, backed by strong analytic capabilities using different data sources, criteria and custom views. The trends of the Key Risk Indicators (KRIs) of your business allows you to detect atypical behaviors (e.g. repeated requests for exceptional rights for a user) and react accordingly. Let's see how >>


Optimize costs
The Evidian IAM Suite allows you to supervise and secure access to Cloud applications while mastering their costs. Accounts for Cloud applications are created dynamically, at the time the user requests access. Evidian Analytics and Intelligence capabilities gives you the means to monitor enrollments to Cloud applications and verify that the costs that are invoiced correspond to your usage.
Orbion
Evidian takes care of everything related to your Identity and Access Management with Orbion (Identity as a Service)
Learn more >
Identity Governance and Administration
Manage access and authorization of all your users in your company
Learn more >
Web Access Manager
Gateway for web apps with SSO, multi-factor authentication, identity federation
Learn more >
Authentication Manager
Authentication Manager
Enterprise multi-factor & passwordless authentication on Windows PCs
Learn more >
Enterprise Single Sign-On (SSO)
Secure access to legacy and web apps on PCs & mobiles with SSO