Login to multiple computers at once
One user authenticates on multiple PCs at the same time with Evidian Authentication Manager
Demonstration of one user authenticating on multiple PCs at the same time
Some employees need multiple PCs and monitors in order to work. These may include trading room workers, control room operators in industry, in transport, in video surveillance and others. It is unrealistic to ask these employees to log in to (and log out from) each PC. Evidian offers a cluster solution with a single login to multiple computers at once.
This cluster solution is compatible with all available authentication methods of Authentication Manager (passive and active RFID, smart card, biometrics and passwords).
How does a login to multiple computers at the same time work?
The cluster solution
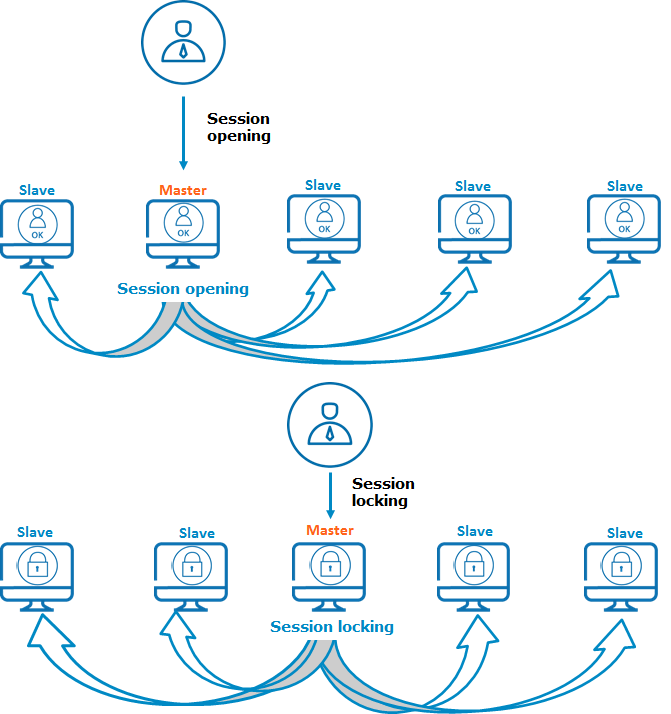
A cluster is a set of computers on which the Windows sessions are synchronized by Evidian Authentication Manager. Operations that a user performs on the Windows session (opening, closing, locking, unlocking) are automatically and simultaneously performed on all computers of the cluster, as illustrated in the figure. When a user performs an operation (opening, closing, locking, unlocking) on a computer, this computer becomes the master and periodically informs the slaves so that they can reproduce the operation.
Session opening / session unlocking
When a user opens a session on a computer of the cluster, all the sessions of other computers of the cluster open with the same user account.
- If a slave computer is not reachable at session opening on the master, the session opening operation on this slave will be performed as soon as the network is restored.
- If a slave computer restarts, and if the last operation performed on the master is a session opening, a session will be opened on this slave computer as soon as it is available.
Session locking / session closing / reboot
- When a computer is locked, all the other computers are locked according to their defined lock mode.
- If a slave computer with an open session does not receive any information from the master for a period of 30 seconds, it is automatically locked.
- When the user closes a computer, all the other computers of the cluster are closed.
- The user can decide to reboot one or several computers of his/her choice or the whole cluster at once.
Users working with the cluster solution can delegate their access to each other without sharing passwords.
Cluster operating principle
Evidian Authentication Manager replaces passwords by strong authentication methods.
Cover all authentication scenarios, whether a user accesses one or several PCs, or several users share one PC.
Examples of single sign-on solutions with Evidian Enterprise SSO and Authentication Manager
Typical use of SSO by over 5 million employees
Employees use a passwordless strong authentication method. After that, application passwords are automatically entered, on behalf of the employee, during application login prompts. This works either with web based, desktop as well as legacy applications without modifying them. Evidian gives an access to the applications to which the employee is entitled. And it transparently modifies and manages strong passwords for each application. An access log is centralized to facilitate audits, to know which employee uses which application and to meet regulatory constraints.
One PC - used by several users
Branch employees, sales staff in outlets, workers in manufacturing industry and others share a same PC in their Enterprise. They use a shared account with autologon to access the Windows session without password to save time. However, knowing who authenticated to the PC and at what time cannot be audited. Evidian with its multi-user desktop solves this problem with a fast user switching in a few seconds and a strong authentication method like a RFID badge to unlock the shared session.
One user – using multiple PCs successively
The day-to-day tasks of some employees may require them to move around within a site, such as doctors in a hospital, production managers at an industrial site, store vendors, and others. On each PC, they must log in to access their session and log out. As it takes time, an alternative solution must be found. Evidian offers a simple solution with a roaming session avoiding multiple login.
One user – using multiple PCs at once
Some employees need multiple PCs and monitors in order to work. These may include trading room workers, control room operators in industry, in transport, in video surveillance and others. It is unrealistic to ask these employees a multiple login to all PCs. Evidian offers a solution with a single login to multiple computers at once.
Are you looking for another solution?
Evidian offers many other solutions that will certainly meet your needs. Do not hesitate to contact us.
Passwordless, contactless, handsfree authentication
Evidian Enterprise SSO provides single sign-on to all users, businesses and organizations.
Free your users from remembering and typing passwords and drive your security policy by automating password management.
Why passwordless strong authentication methods?
Passwordless authentication
Passwords are the weak point of many authentication policies. Single or shared Windows passwords create a risk of intrusion and make it almost impossible to precisely verify the use of Windows accounts.
Replace passwords
Replace passwords with strong authentication: devices or biometrics. With Evidian Authentication Manager, users can prove their identity by what they have (smart card), who they are (biometrics) and what they know (password).
2FA - 2 factor authentication (or MFA)
Authentication Manager grants you the capability to use 2 factor authentication (or more). With this feature, your users will have to use 2 methods of authentication in order to login to their Windows session.
Even for sensitive applications
You can use a strong authentication to reauthenticate users when accessing sensitive applications and not only at Windows session login. And this transparently to the application by adding the Enterprise Single Sign-On module.
More than 5 million employees use Evidian authentication products
Most popular authentication |
Description |
|
Simple, even rustic, its biggest flaw is that the security level depends directly on the complexity of the password. The result is that too many overly complex passwords make users take various measures to remember passwords, such as writing them down on Post-It™ notes or entering them in an Excel file or a smartphone.
A login and password combination is the most commonly used method of authentication. Single sign-on (SSO) solutions can reduce the increased number of passwords. |
|
An OTP can prevent a password from being stolen and reused. An OTP system (usually a specialized calculator) provides a password upon request. This password is valid for a limited period of time and can only be used once.OTP is generally used for initial authentication for external access via VPN. It does not require any configuration of the workstation or smartphone concerned. |
|
X.509 certificates are often used to encrypt or sign messages without having to share a secret. The login ID is a public certificate that is signed and therefore guaranteed by a recognized certification authority. The user must provide a secret piece of information in order to use the cryptographic elements, such as the PIN code of its smart card or its USB key. In companies, smart cards are typically used more often than USB keys for authentication, even though the chip itself is often the same in both cases.This solution is frequently used for initial authentication or for access to email or web applications. It requires a Public Key Infrastructure (PKI). |
|
Storing the login and password on a smart card completely secures the authentication process. The password can be very complex, and it can be automatically and randomly changed very frequently. Without the card and its PIN code, there is no longer access to the password.This solution is usually used for authentication on PCs without having to deploy a key infrastructure. |
|
A cell phone can serve as an authentication object. There are two main methods used:
The cell phone method is often used if the user forgets his password or smart card, particularly for access on the Internet. |
|
Authentication using biometrics is based on verifying a part of the user's body. The most often type used is the digital fingerprint. The user's biometric data is stored on a central server (with major legal constraints), on the workstation, or on a smart card.Biometrics is typically used for initial authentication or to protect access to highly sensitive applications. |
|
A chip that is embedded into a contactless card contains a code that identifies a user. Therefore this is an identification method that, paired with a password, can be used in authentication procedures. There are two versions of this technology. With active RFID, the card has its own power unit. This enables detection over a longer range (e.g. when entering a room or office).Active RFID can be used to detect absence for workstations in areas accessible to the general public.With passive RFID (HID, MIFARE, etc.), the card does not have its own power unit. When it is read, it is powered by an electromagnetic field generated by the reader.Passive RFID is often used to control physical access using a pass or for payment in a company cafeteria. This type of card can be detected from a few centimeters away |
Orbion
Evidian takes care of everything related to your Identity and Access Management with Orbion (Identity as a Service)
Learn more >
Identity Governance and Administration
Manage access and authorization of all your users in your company
Learn more >
Web Access Manager
Gateway for web apps with SSO, multi-factor authentication, identity federation
Learn more >
Authentication Manager
Authentication Manager
Enterprise multi-factor & passwordless authentication on Windows PCs
Learn more >
Enterprise Single Sign-On (SSO)
Secure access to legacy and web apps on PCs & mobiles with SSO