What is the Web SSO?
Unique web authentication, known as the Web Single Sign-On, allows users to proceed using a Single Sign-On to access a group of web servers that require authentication.
The Web SSO considerably reduces the risk of losing usernames, and limits the number of helpdesk calls for locked-out users. Users no longer have to remember a large number of usernames and passwords for web servers with different technology.
The Web SSO therefore benefits users by simplifying access, and benefits the company by lightening the application support load.
Web SSO technologies
There are mainly two different techniques for setting up the Web SSO:
- SSO management within the web application or by using agents in protected applications.
- SSO management upstream of the web application, using a web-based reverse proxy to control authentication information within the application, as secondary authentication data.
Agents
Authentication requests are intercepted by an Agent module that must be inserted into the application. This agent takes cares of authentication and management of the application access control. This technology has several drawbacks:
- The applications must be modified for the purposes of the SSO agent. This depends on the web application technology and the operating system, and is often impossible with proprietary applications.
- The application must be directly visible from the user's web browser. When the user is on the web, that means the application is directly published on the web.
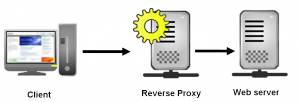
Reverse proxies
An intermediate server, the reverse proxy, acts as a contact point between the user's web browser and the web server requiring protection.
The reverse proxy masks the protected web server by presenting different external URLs to the internal URLs. It becomes the communication point and can control access and carry out Single Sign-On operations. Ideally, it is not necessary to modify the protected application.
Nevertheless, this technology does have some drawbacks:
- The web application must be correctly written and contain clean URLs, and the URLs must be relative to the root of the website. Most reverse proxies only modify the HTTP headers and are not able to modify the HTML content of the pages.
- The advent of AJAX technologies and URL and Javascript modifications make it difficult for reverse proxies to analyse page links and reconstruct external URLs.
- The web application should not contain absolute links to other internal applications which are also accessible behind a reverse proxy.
However, it also has several advantages:
- It's completely independent of the web servers, both technically and environmentally.
- Several reverse proxies can protect the same web server and provide high availability and load balancing of the access points.
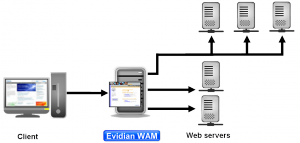
Web SSO technology in Evidian Web Access Manager
Evidian Web Access Manager is based on the use of intelligent reverse proxies.
Evidian Web Access Manager uses reverse-proxy technology, capable of deep processing of HTTP feeds between the user's browser and the protected web server.
Web Access Manager Architecture
Web Access Manager uses configurable web proxies in three different modes, depending on usage constraints and the applications protected:
- "Portal" mode – one instance of a reverse proxy is used to protect several web applications. The external URL "http://wam.domain.com/app1" protects application 1; the external URL "http://wam.domain.com/app2" protects application 2. Evidian Web Access Manager carries out all the URL translations required to keep all URLs consistent.
- "Remote web agent" mode – one instance of a reverse proxy is used to protect a single application. The external URL "http://wam.domain.com/" protects a single application, and the URL translations take place within the application's web pages to ensure that no internal URLs are published externally.
- "Local web agent" mode – one instance of a reverse proxy is used on the same machine as the application to be protected. The reverse proxy must use the application's TCP port, and the application must be moved to another port or alias address on the machine. The reverse proxy only carries out a single minimal translation in the HTTP feed. This configuration has the drawback of affecting the configuration of the protected application, and is therefore used in specific cases only. Generally it is not applicable.
All these configurations can be combined. Evidian Web Access Manager supports the possibility of configuring, deploying, and administering several "portals" and "agents" in the same configuration, on one or more machines, administered from a single console.
The web SSO of Evidian Web Access Manager is non-intrusive for web applications.
A powerful processor for HTTP requests and responses
The core of Evidian Web Access Manager is based on analysing all the requests that pass between the client and the server. The request processor carries out the following tasks:
- Determines whether primary authentication is necessary.
- Carries out access control, filtering and authorisations.
- Does an in-depth analysis of the content of requests and responses.
- Carries out URL translations and content modifications for protocol headers.
- Carries out secondary authentications and adds data to the HTTP feed.
Orbion
Evidian takes care of everything related to your Identity and Access Management with Orbion (Identity as a Service)
Learn more >
Identity Governance and Administration
Manage access and authorization of all your users in your company
Learn more >
Web Access Manager
Gateway for web apps with SSO, multi-factor authentication, identity federation
Learn more >
Authentication Manager
Authentication Manager
Enterprise multi-factor & passwordless authentication on Windows PCs
Learn more >
Enterprise Single Sign-On (SSO)
Secure access to legacy and web apps on PCs & mobiles with SSO