60% of users
have undue access right
25% of the breaches
involved internal actors
Identity Governance and Administration
Evidian Identity Governance and Administration leverages your organization by getting your Identity Management processes accurate, efficient and reliable.
- Identify and manage all the users accessing to your applications
- Make operational people owners of access and rights decisions
- Reduce operational risk and ensure compliance
- Define and Implement a security and operational policy
- Speed up delivery of access to the required business applications

Zero Trust: Do your users have the required level of accreditation to access the applications?
How to ensure that users accessing an application are accredited with required training, certification, charter signature, and how to ensure that this accreditation is still valid?
In many organizations, particularly in healthcare, defense, and finance, access to applications doesn’t depend solely on the user's business profile but also on their level of accreditation. A certain level of accreditation (training, certification, signing a charter) may be required to be in compliance with current legislations, insurance, company charters, etc.
During audits, compliance reports may also be requested.
To meet these requirements, Evidian IGA integrates a new feature to verify when assigning rights that a user has the required level of accreditation. This feature also makes it possible to take into account changes in the level of accreditation over time: granting rights upon obtaining accreditation or revoking them upon expiration of accreditation.
For more informations contact us.
Be agile and reliable in your Business
Evidian Identity Governance and Administration is a comprehensive and easy to deploy Identity and Access Governance solution that provides customers with many benefits.
Operational Risk management - Efficiency and operational cost reduction
Improved governance - Availability & standardization - Easy deployment
LEARN MORE
Operational Risk Management
To meet the challenges of insider threat and illegitimate access, Evidian IGA provides a comprehensive set of governance capabilities to enable organizations to mitigate operational risks and comply with security policies and regulations.
Customers can enforce their user rights assignment policy with a unified view of their users’ identities. Evidian IGA entitlement assignation engine is based on the Extended Role Based Access Control model (Extended RBAC).
Evidian IGA ensures data consistency by centralizing identities from various sources, allowing Security Officers to base their policy on a unified and reliable identity source.
The Access Certification feature provides an effective way to review entitlement according the least privilege principle. Security Officers can target rights and applications based on a pre-defined risk profile, ranging from non-critical to critical.
Hence Access Certification Campaigns can focus primarily on rights and application that could put the company at risk. Campaign monitoring dashboards allow you to manage effectively campaign progress.
Improved Governance
Customers using Evidian Identity Governance and Administration benefit from a set of predefined reports designed to provide proofs of governance and compliance in managing their Information System.
More than 45 report types are included with the solution to cover 7 areas in the system’s governance: Policy Status, User Lifecycle, Policy Analytics, KPIs & Quality, Activity, Reconciliation & Certification, and Personal Data.
The Reports layout, language and export format are fully configurable prior to being signed and sent to the appropriate persons within the organization.
Go further in your analysis and risk management with Analytics and Intelligence.
Efficiency and Operational Cost Reduction
Evidian Identity Governance and Administration allow customers to manage easily their users’ Identity Life Cycle (e.g. arrivals, changes, departures etc.) without imposing tedious and time-consuming administration tasks; tasks that can also lead to human errors.
Organizations can speed up the delivery of access to business applications with the solution’s automatic provisioning capabilities, and improve user productivity by simplifying access to authorized applications wherever they may be. Process automation and self-service features allow to reduce administration costs and optimize the return on investment of the solution.
Evidian Identity Governance and Administration also supports hybrid environments in a secure and cost-effective way.
Customers can manage accounts without having to worry about synchronization delays between the on-premises and Cloud identity sources.
Moreover, since applications licenses are also managed through the security policy, Evidian Identity Governance and Administration customers can also manage license costs and take advantage of the reporting features for auditing costs.
Availability & standardization
Deploy a Corporate IAM policy
Organizations can now consider deploying Group’s security policy and processes through an IAM implementation even if subsidiaries have not reached the critical size to benefit from a local IAM solution. The Evidian proposal with a Shared IAM will let you centrally deploy Evidian IGA solution to be used by each subsidiary. The solution improves and standardizes the Group’s security policy and processes, while respecting the specific functions of each subsidiary, facilitating the adoption. This model optimizes implementation and operating costs. (Up to 25% savings compared to unit solutions at each subsidiary).
Easy deployment
Smooth deployment is a key for the success of any IAM project.
With Evidian Identity Governance and Administration, customers can foresee a more controlled and cheaper deployment with the new workflow driven provisioning and configuration feature.
During the deployment, automatic onboarding of applications is easy and templates management no longer requires extra operations.
In Evidian IGA, approval behaviors are no longer linked to the workflow configuration and can be configured for each identity source.
The solution includes built-in features to support all use cases for Identity Life Cycle patterns with more than 40 workflow processes available. The solution also offers an organization model to easily implement delegated administration.
Governance and Automation
Evidian Identity Governance and Administration lets you manage the entire identities life cycle management.
Identity management - Security Policy definition
End user self-service and process management
Access management to applications - Compliance & Reporting
LEARN MORE
Identity management
- Creation of a centralized repository of digital identities
- Multiple types of information sources: HR systems, LDAP Directories, CSV/XLS files…
- Non-intrusive with sources of identity information
- Capacity to automatically launch Identity Management processes based on detection of changes
- Capacity to follow enterprise evolutions; very easy to add/remove organizations
- Simulation capability and Threshold management
- IAM for multi-entity groups
Security Policy definition
- Security policy based on RBAC (Role-Based Access Control) model extended with Organizations, Contexts and Business Rules
- User entitlement based on role assignment, role-organization couple, exceptions or “same as another user”
- Dynamic role assignment based on user attribute values and time constraints
- Management of risks (SOD) at user entitlement and role content definition
- Centralized or distributed administration
- Simulation capability, Central audit & reporting features
End user self-service and process management
- End-user self-service portal; password reset, white pages, access requests, validation
- Ready to use set of Identity & User entitlement management processes
- Dynamic customization of the data and pages structure based on the user’s needs
- User entitlement management delegated to the Business
- Workflow actors & sequence based on Security Policy, no need to modify workflow process itself
- Capacity to modify workflow processes structure with the “Workflow Editor” option
Access management to applications
- Several Authentication Methods; Kerberos, Social Authentication, Strong Authentication, QREntry
- End User activation
- Standard connectors; LDAP, SQL, CSV, AD, Lotus Notes, SAP, GCOS, IBM RACF, SalesForce, Google Apps, ServiceNow, Office 365 & Generic connectors...
- Capacity to manage AD & RACF low level permissions, e.g. printers, shared resources
- Several processes to tailor provisioning actions
- Reconciliation process to check the compliance with the defined policy
- Integration with CyberArk & Wallix PAM tools
- Integration with Service Now ITSSM
Compliance
- Access Certification campaigns
- Ability to set a range of risk levels associated with the access rights to be certified, as a choice criterion
- Definition of multiple levels of responsibility
- Monitoring of campaign progress
- Related reports
Reporting
- Policy Status: provides status on the policy objects of your solution
- User Lifecycle: provides information about user arrivals and departures
- Statistics: helps you monitor the use of the policy
- KPI – Quality: gives you Key Performance Indicators (KPIs) and Quality information on the policy you defined for your solution
- Activity: helps you monitor the user activity
- Certification: provides general and detailed information of Certification Campaigns results
- GDPR: provides user information with respect to GDPR regulation
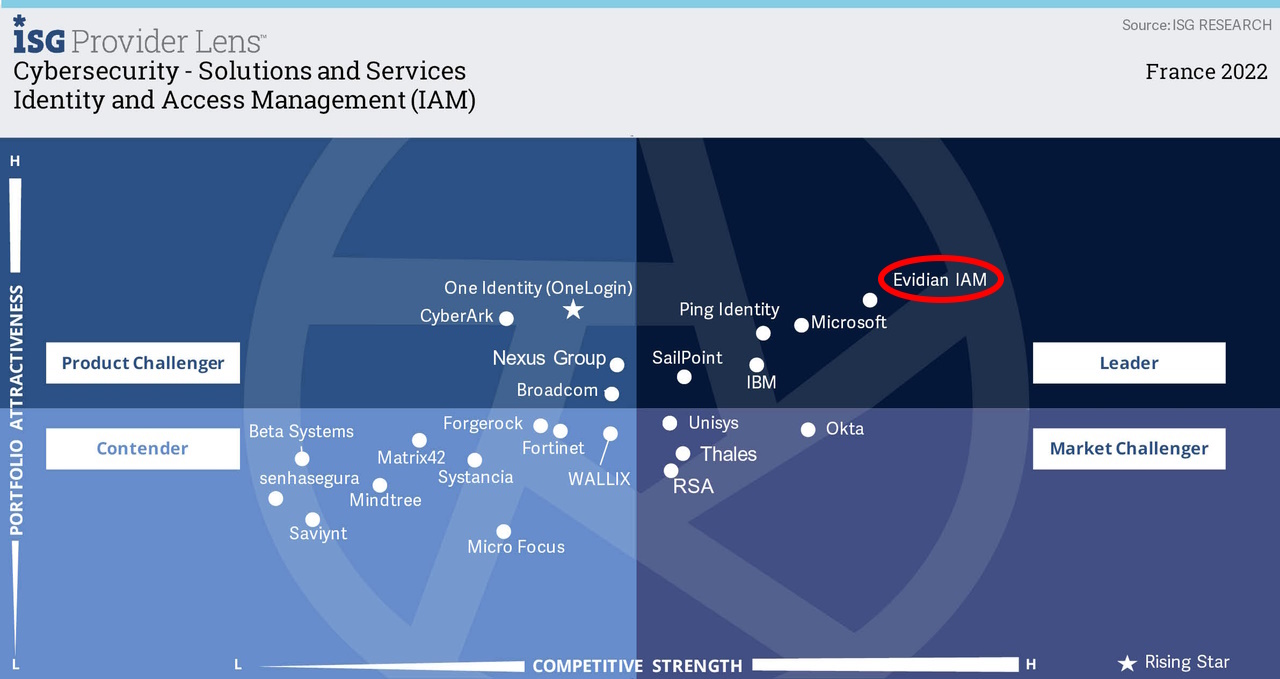
Certification and compliance
Related products
Analytics and Intelligence
Effective cybersecurity now demands automation and analytics to work in conjunction for threat identification, mitigation and management. As businesses move to become digital enterprises they must continually scrutinize their operations, security processes and IT environments.
- Transforms access and identity raw data into actionable intelligence
- In line with compliance regulations, business security policies & corporate risk management objective
- Tracks down and analyze access data
- Extracts trends to report
- Acts to improve right assignment management policy
ID Synchronization for a multi-directory identity repository
User information is often stored in many places: Active Directory, HR applications, Oracle and SQL Server, e-mail base, LDAP sources…
How to get a single, reliable identity repository?
By reconciling existing sources automatically, directory synchronization helps to maintain a central identity repository for all users.
- Create a single trusted identity repository
- Draw information from the most reliable sources
- Retain your existing procedures
- Improve the quality of all your user databases
Orbion
Evidian takes care of everything related to your Identity and Access Management with Orbion (Identity as a Service)
Learn more >
Identity Governance and Administration
Manage access and authorization of all your users in your company
Learn more >
Web Access Manager
Gateway for web apps with SSO, multi-factor authentication, identity federation
Learn more >
Authentication Manager
Authentication Manager
Enterprise multi-factor & passwordless authentication on Windows PCs
Learn more >
Enterprise Single Sign-On (SSO)
Secure access to legacy and web apps on PCs & mobiles with SSO