-
Web Access Manager
Gateway for web apps with SSO, multi-factor authentication, identity federation
-
-
Orbion - Identity as a Service
Evidian WAM also secures access to all applications in SaaS mode
80% of all organizations
experience at least
one compromised account threat per month
3 companies out of 4
let their employees use their own device
to access business applications
70% of SSO transactions
emanate from on-prem apps as of today,
while modern federation protocols are expected
to account for 60% by 2022
SSO & Identity Federation
A modern IT landscape relies more and more on Cloud apps. However on-prem apps largely prevail. Evidian Web Access Manager (WAM) enables you to transparently address access challenges for both environments.
While security remains your main concern, users expect a totally frictionless experience in their corporate digital journey, indifferently using corporate assets, their own devices from inside the entreprise realm or directly from the internet.
Evidian WAM is also available as a service in our Orbion solution.
-
SSO for all web resources (Legacy, Modern, Mobile; APIs...)
-
Leverage modern Federation protocols
-
Embedded access gateway/portal
-
Adaptive multi-factor authentication
-
Granular access policies
- Dynamic & Configurable dashboards for Audit and compliance
Security and user convenience
Protect and enable employees, contractors, partners and customers with Evidian WAM.
Tackle all access challenges - Enhance user experience
Leverage Identity Management - Increase agility & business value
Improve your budget - Comply with regulations
READ MORE
Tackle all access challenges
- Federation engine to access all existing and future Cloud applications
- Authentication to native mobile apps thanks to formal internet standards
- Easy integration of legacy on-prem apps into your access strategy
- API protection lets you securely open your IT
- A centralized policy engine means consistent access control for all web ressources
Enhance user experience
- Embedded portal that aggregates all sanctioned apps and services a user can access
- Transparent SSO ensures a secure and pleasant digital journey wherever the user connects from
- The self-service user interface avoids calling the helpdesk for password recovery or authentication methods enrollment
- Social IDs ease registration and authentication of your customers
Leverage Identity Management
- Self-registration allows joiners to create their own identity in the Identity Management solution
- Tight relationship between Evidian WAM and IGA ensure access rights are always in sync with assigned roles
- Recertification in Evidian IGA can be capitalized to dynamically adjust access policy
Increase agility & business value
- Easily integrate your partners into your access strategy
- The "connect SDK" easily turns any existing webpage into a custom-made access portal
- Future-proof for on-premise, cloud and mobile applications, as well as new services
- Integrated multi-factor authentication eases the burden of delivering enhanced security
Improve your budget
- Fewer helpdesk calls thanks to integrated password recovery and self-service facilities
- SSO and multi-factor authentication decrease the risk of data loss and compromised passwords
In conjunction with IGA, "Just in Time Provisioning" lets cut costs for unused SaaS licenses - Central point of management for all access
- High Availability for resillent deployments with lower downtime
Comply with regulations
WAM allows to track audits events: authentication and any user request or administrators actions.
The solution becomes a key enabler for compliance as it answers most technical challenges sets by the EU’s GDPR.
Customer Identity Access Management
with Evidian Suite
Develop business while building trust and increasing your knowledge of the customers
- Let your customers register with their social identity in a frictionless manner
- Seamlessly add CIAM features to your existing web site with our integration kit
- Secure critical user actions with second factor step-up authentication thanks to Evidian Authenticator for mobile app
- Comply with regulations to respect consumer privacy and control of their personal data
- Know your customer: gather profile data synchronously or asynchronously
- Enrich your analytics with our Google Analytics connector

Cloud Identity Security
Cloud Identity Security by Evidian is our offer to align your Identity and Access Management with your Cloud strategy. It allows to automatically provision (and de-provision) user accounts to Cloud providers, as well as creating and managing service accounts without any impact on your Cloud applications. It also permits to leverage your identity repository: on-prem AD, Azure AD or any other directory. By default the Principle of Least Privilege is applied and a set of predefined roles is proposed for immediate take-off. Accesses are protected across all your IT, Cloud, SaaS, on-prem with transparent SSO and strong multi-factor Authentication methods.
- Adopt Identity Governance and Administration for your SaaS and cloud environments from a single point of administration
- Granularly control who accesses any of your Cloud assets from one central point
- Embrace multi-cloud and hybrid-cloud capabilities without multiplying your identity repositories and policies
- Invite your partners to securely access your cloud ecosystem with full control and traceability
- Always ensure your organization changes are reflected in your Cloud strategy
- Prevent identity sprawl for your users
- Get rid of weak passwords with Second Factor and Multi-Factor authentication
- Let your users autonomously manage their strong authentication means
Web resources protection, the right way
Your resources deserve the best protection. Nowadays, a company's IT assets tend to be mainly web accessible, yet there is a variety of such services: modern web applications, REST APIs, legacy web resources, mobile apps...
And that is to be combined with other parameters: do we speak about homebrew applications? hosted on-premises or in the cloud? SaaS applications? Accessed from a PC, a tablet, an iPhone or a Chromebook?... Evidian Web Access Manager is a versatile solution that helps you answer these challenges... and more!
Identity federation - API protection - Next generation authentication - Single Sign-on
Customer IAM Connect Toolkit - Web portal - Embbeded security - Logging and Audits
Detecting and blocking dangerous behaviors
READ MORE
Identity federation to secure your SaaS/Cloud assets
From a simple central point of access to your SaaS business applications to complex scenarios involving suppliers and consumers, keep control of your important assets.
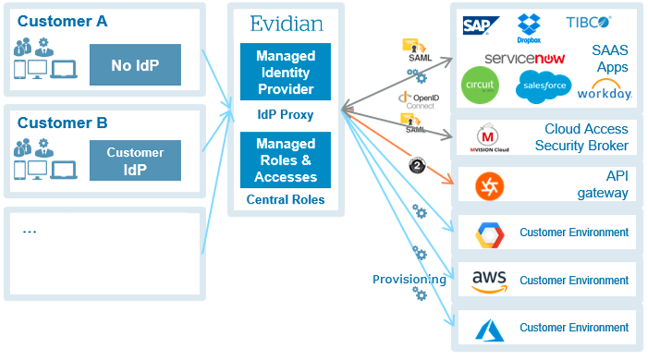
Evidian WAM extensively supports Identity Federation standards, acting as an Identity provider to authenticate internal users toward SaaS apps, as a service provider to let you securely publish your own services or even as an IdP proxy to allow your partners' users access your resources in a trustworthy way.
API protection for a modern IT
REST APIs are the way toward modernization, either to create custom applications or to open your IT to the outer world.
Delegate the burden of protecting your APIs to Evidian Web Access Manager: it can both manage API authorization with OAuth 2.0 and let you securely publish your APIs with access protection, ensuring only the right ressources are accessed by the right app at any time.
Next generation authentication
Passwords have been identified as a vector of data breach for a long time now.
Evidian WAM comes with a large catalog of embedded authentication methods. From simple OTP, X509 certificates, TOTP to next generation authentication means : patented challenge-response Evidian GridCard, Evidian QRentry (QRcode generated OTP), Push Authentication with Evidian Authenticator mobile app, as well as the new Fido 2 standard. Third party authentication services (such as Gemalto, RSA, Double Octopus, ...) can also be seamlessly integrated.
All these methods can be combined to create stronger authentication scenarios. In addition Evidian comes with Adaptive Authentication and step-up that let you decide which method a user should use according to his location, the time of the day, his browsing environment and the ressource he is trying to access.
SSO (Single Sign-on) to legacy, cloud, mobile apps
Security is not all about encryption, all security strategies must take into account the human factor. Today, the average internet user possesses more than one hundred online accounts, which means just a few passwords to remember and a lot of associated poor behaviors (password re-use, weak password, password sharing, etc...).
Leveraging Evidian universal SSO combined with strong authentication, drastically diminishes your exposed attack surface and makes it much harder to exploit compromised credentials. In the meantime user experience is enhanced : one unique point of access whatever the location, whatever the device, to access all his work tools.
Customer IAM Connect Toolkit: seamless and secure digital experience
With the embedded "CIAM Connect Toolkit", easily integrate customer oriented functionalities into your existing public website. More than half of the consumers give up registration when facing classical forms, let them authenticate with their social identity (from Google, LinkedIn or any other). Existing users are not forgotten and will be able to link their current account with the social ID of their choice.
Include bot protection with captcha and email verification. Privacy and trust are always our concern, the solution comes with consent management and a fully featured self-service account management interface.
Provided APIs will let you gather user data in your marketing tools, synchronously and asynchronously. And, at last, just add your Google Analytics ID to the configuration, to enrich your dashboards with CIAM related events (creation, authentication, profile modification, and so on).
Web portal: tailored for all devices and fully customizable
Transform an existing page into an access portal or start from scratch, in both cases Evidian Web Access Manager can help you. It comes with an integrated access portal, encompassing a self-service user portal and access links to authorized services, plus a personal list of user preferred services.
Alternatively you can take advantage of the included Integration SDK to seamlessly add these features to an existing website such as your intranet, while inheriting from your organization styling.
Embbeded security
Web Access Manager is built for modern web security. It offers a wide variety of authentication methods, access control to different Web resources, SSO...
By allowing a fine tuning of the SSL protocol (protocol, encryptions…) and Certificates (CRL, OSCP…), administrators can secure the stream of information with the highest security level.
No plugin is necessary for Web browsers and cookies cannot be modified. You can also apply IP filtering on workstations accessing WAM services and use the available APIs to extend the WAM features.
Auto-administration of WAM main functions secures user behaviors and limits the need for help desk calls. The autonomous user does not need to contact a third party and provide sensitive information to get assistance. This function includes the following:
- Change password
- Reset password, by Q&A, OTP,…
- Self-enrollment in WAM
- Deprovisioning of users
- Administrators can be given roles allowing a fine-grained right management system on possible operations
Logging and Audits
Evidian WAM with Evidian Analytics & Intelligence provide a comprehensive auditing infrastructure, with reports and predefined dashboards on events pertaining to administration, authentication, application access and SSO key quality indicators. Security audit events are also generated for each user action, thus enabling to track risky behaviors or just display information regarding the usage of the solution.
All requests (GET, POST,…) are traced in log files. A rotation mechanism can also be configured for the size and length of these files. You can also push this data towards a Syslog infrastructure.
Detecting and blocking dangerous behaviors
WAM can apply a common password policy to all WAM portals (and to all possible user populations). This policy enables to define the following elements:
- Frequency of primary password change by the user: at any time or with a configurable delay between two modifications.
- Frequency of primary password change forced by Web Access Manager: the password never expires or the periodicity configurable in days of forced password modification.
- Delay in seconds the user will have to wait for in case of bad login before being able to reauthenticate.
- Maximum number of bad logins before the user account is blocked (WAM level).
- How this account will be unblocked: by the WAM administrator or automatically after a configured period of time (in minutes, hours or days).
WAM also enables users to reset their primary password through a classic Q&A mechanism. If he has forgotten his password, the user will be able to reset it after being identified and having answered correctly the questions he has chosen beforehand.
Analytics for Evidian WAM
Analytics reinforces the Evidian Web Access Manager offer by collecting the audit trails generated by the Evidian WAM product. It sorts and enriches them in order to generate a synthetic representation while respecting the compliance requirements, business security policies and risk management objectives of the business.
Its ergonomic and dynamic web interface provides you with dashboards (Application Accesses, Audit Activity, Password changes, User Authentication Activity...) that allow you to view and analyze events relating to the activity of your users. Thanks to Analytics for WAM, you will be able to determine trends, investigate the origin of a problem, assess a level of risk or even meet a regulatory requirement.
Some examples of dashboards:
- Application Access : displays information regarding application accesses in WAM (User name, Service, Date, Successful / Unsuccessful accesses...).
- Password changes : displays information regarding password changes events occurred in WAM (Requester of the password change, Name of the user for whom the password is changed...).

Evidian Access Management certified by McAfee
Trustway for data protection and Evidian for access management are compatible with the McAfee Cloud access security broker CASB. The combined offer ensures greater control to customers for their data encryption and Identity and Access Management needs across their multi-cloud environment.

Unified cloud identity and access management solution for ultimate security
Acting as a single identity provider and management system for all platforms, cloud and on-premise, this new solution, based on Evidian software, enables organizations to keep control of all identities that need access to their business systems, providing them with ultimate security.
Certification and Compliance
Orbion
Evidian takes care of everything related to your Identity and Access Management with Orbion (Identity as a Service)
Learn more >
Identity Governance and Administration
Manage access and authorization of all your users in your company
Learn more >
Web Access Manager
Gateway for web apps with SSO, multi-factor authentication, identity federation
Learn more >
Authentication Manager
Authentication Manager
Enterprise multi-factor & passwordless authentication on Windows PCs
Learn more >
Enterprise Single Sign-On (SSO)
Secure access to legacy and web apps on PCs & mobiles with SSO